AI-Powered Chat Assistant for Compliance & Audits
Bandiz AI simplifies regulatory audits with automation, offering real-time compliance guidance via WhatsApp and Telegram for seamless, efficient audit processes.
The Smart AI Voice Agent for Consent Management
Tom, an AI voice agent, ensures seamless, compliant consent management in English and Hindi, enhancing transparency, trust, and regulatory compliance.
Protect, Detect, and Secure Your Critical Data
PII Data Scanner detects sensitive data offline, ensuring privacy and security while helping businesses and individuals manage and protect information.
AI-Powered Chat Assistant for Compliance & Audits
Meet Bandiz AI, your intelligent compliance assistant designed to simplify and automate complex regulatory audits. Operating through WhatsApp and Telegram, Bandiz AI provides real-time responses and expert guidance on compliance-related queries, ensuring seamless and efficient audits.
- Multi-Platform Support – Available on WhatsApp & Telegram for instant access.
- Comprehensive Compliance Expertise – Handles DPDP, ISO 27001, SOC 2, and other regulatory audits.
- Process Security Documentation – Generates, reviews, and organizes essential compliance documents.
- Real-Time AI Insights – Provides accurate compliance assistance on demand.
- Audit Automation – Streamlines the entire audit process with AI-driven intelligence.
- Secure & Reliable – Ensures compliance with industry standards and data security best practices.
- DPDP Audits – Assess compliance with the Digital Personal Data Protection Act.
- ISO 27001 Audits – Ensure adherence to international information security standards.
- SOC 2 Audits – Evaluate data security, privacy, and organizational controls.
- Regulatory Audits – Stay compliant with evolving industry regulations.
- Security Documentation – Automate policy generation, risk assessments, and compliance reports.
- Pre-requisite: A Telegram account must be set up and accessible, as the AI chat assistant runs and communicates through the Telegram platform.
- Initiate a Chat – Connect via WhatsApp or Telegram.
- Ask Your Queries – Get instant responses on audits & compliance.
- Generate Reports – AI-driven analysis for compliance documentation.
- Track Audit Progress – Monitor and complete audits effortlessly.
Click below to experience AI-powered compliance auditing like never before.
🔒Automate Audits. Ensure Compliance. Stay Secure with Bandiz AI!

The Smart AI Voice Agent for Consent Management
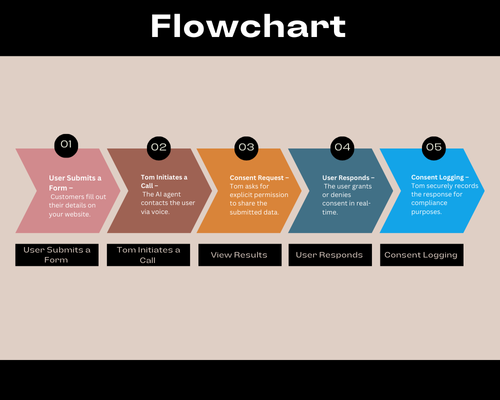
Data privacy matters! Tom is an intelligent AI-powered conversational voice agent designed to ensure seamless and compliant consent management for your website.
With support for both English and Hindi, Tom engages with customers and end-users in real-time to confirm their consent before sharing their submitted details with your website. This ensures transparency, compliance, and trust in every interaction.
- Automated Consent Verification – AI-driven voice interactions to obtain user permission.
- Bilingual Support – Communicates fluently in English & Hindi for wider accessibility.
- Seamless User Experience – Ensures a smooth and non-intrusive consent process.
- Enhanced Data Privacy – Strengthens compliance with privacy regulations.
- Real-Time Confirmation – Instantly validates and records user consent.
- Scalable & Adaptive – Easily integrates with websites and business workflows.
User Submits a Form – Customers fill out their details on your website.
Tom Initiates a Call – The AI agent contacts the user via voice.
Consent Request – Tom asks for explicit permission to share the submitted data.
User Responds – The user grants or denies consent in real-time.
Consent Logging – Tom securely records the response for compliance purposes.
Click below to integrate Tom – Your AI Consent Manager and enhance your data privacy strategy.
Learn More—>
🔒Empower Your Users. Protect Their Data. Build Trust with Tom!

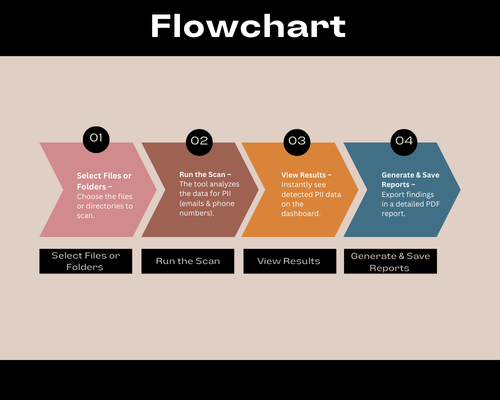
PII Data Scanner – Protect, Detect, and Secure Your Critical Data
In today’s digital world, safeguarding sensitive information is more important than ever. Introducing PII Data Scanner, an advanced tool designed to scan files and folders within your system environment to detect Personally Identifiable Information (PII) such as email addresses and phone numbers.
This powerful software operates in offline mode entirely within your machine, ensuring 100% privacy and security without exposing your data to external networks. With an intuitive interface and rapid scanning capabilities, it helps businesses, security teams, and individuals identify, manage, and secure their PII data effortlessly.
- Compliance & Data Protection – Ensure regulatory compliance (GDPR, CCPA, HIPAA) by identifying stored PII.
- Prevent Data Leaks – Discover and secure sensitive data before it becomes a risk.
- Efficient Data Audits – Automate and streamline PII detection for security teams and enterprises.
- Enhanced Privacy – Keep confidential information within your system with zero data exposure.
This tool is currently in its 1/10th version, providing an initial glimpse of its potential. The final version will be significantly more accurate, faster, and equipped with an enhanced user-friendly GUI. Future updates will also include customization options tailored to clients’ needs, ensuring a seamless and efficient experience.

AI-Driven Compliance Solutions: Protecting Data Privacy and Managed Cloud Service and DevOps
Testimonials


Bringing the best Data Security Vendor Solutions to you.
Working only with the best, to ensure the quality of our services, and to bring state of the art technology to those who need it.
Your IT Challenges
Datacenter & Hosting
Our facility – Data Center – is the first in the USA that meets the strict ANSI/TIA-942 rated 4 certificate requirements for design, build and operate.
Amazon Web Services (AWS)
Microsoft Azure
RackSpace
OVH
DigitalOcean
Bluehost
![]()
Collaboration
Despite modern cloud technology, your users operate in a familiar Microsoft Office environment and benefit from broad compatibility and low-threshold access.
Exchange Online
Sharepoint Online
Defender for 365
Autopilot
Office Apps
Windows 365
![]()
Cloud Plattform
Customized cloud platform designed to improve performance, lower IT costs, and provide secure and reliable access to your company data from any device, anytime, anywhere.
Amazon Web Services (AWS)
Microsoft Azure
Google Cloud Platform (GCP)
Oracle Cloud
IBM Cloud (Kyndryl)
Linode (Akamai)
![]()
Network & Connectivity
Network topologies include hub, linear, tree, and star designs, each of which is set up differently to promote connectivity between computers or devices.
CiscoSophosWatchguard
Extreme Networks
Dell Technologies
VMware
Recovery
Veeam
Altaro
Acronis
Zerto
![]()
Success Stories
Solving Data Security challenges in every industry, every day.

Industry & Manufacturing

Transportation & Logistics

Healthcare

Banks & Insurance

Consulting Providers

Non-Profit


























Partner with Us for Data Protection Consulting and Data Privacy Advisory
We’re happy to answer any questions you may have and help you determine which of our services best fit your needs.
Your benefits:
- Client-oriented
- Independent
- Competent
- Results-driven
- Problem-solving
- Transparent
What happens next?
We Schedule a call at your convenience
We do a discovery and consulting meting
We prepare a proposal
Schedule a Free Consultation
Recognized by the best
Industry leaders trust us to excel in solving data security challenges. Our expertise ensures top-notch privacy governance and compliance solutions for all.